Economical & Best CCNA, MCITP, CCNP, CCIE, Ethical Hacking, LINUX Training in Hyderabad from Industry top Trainers.
Friday, January 25, 2013
Saturday, January 12, 2013
Under the hood of recent DDoS Attack on U.S. Banks
Incapsula security study reveals how a simple neglect in managing the administrative password of a small UK site was quickly exploited by Botnet shepherds operating obscurely out of Turkey to hurl large amounts of traffic at American banks.
If you've been following the news, you are probably aware of a wave of DDoS attacks that recently hit several major U.S. banks. Izz ad-Din al-Qassam, a hacker group that claimed responsibility for these attacks, declared them to be a retaliation for an anti-Islam video that mocked the Prophet Muhammad and a part of the on-going “Operation Ababil.”
As the reports of the attack started to roll in, Incapsula security team was able to uncover one of the secret foot-soldiers behind the assault: a compromised general-interest UK-based website that was trying to hurl large chunks of junk traffic at three of the world's largest financial institutions (PNC, HSBC and Fifth Third Bank).
At On the eve of the attack, this website suddenly became a focal point of a rapidly -increasing number of security events, caused by numerous requests with encoded PHP code payload. Incapsula was able to intercept these requests and traced them back to a backdoor shell that was used to hijack the site.
The backdoor was installed before the website on-boarded Incapsula, and yet the cause of security breach was clear. The administrative password was...you guessed it: admin / admin.
After decoding the incoming PHP requests, the security team could clearly identify them as DDoS attack commands, originating from a Turkish web design company website which was used as a remote Botnet C&C. From the looks of it, the Turkish website was also compromised and used as an additional buffer between the real hacker and its U.S. based targets.
Further investigation showed that the UK website was a part of a Botnet for Hire which was working in “shifts” to produce HTTP and UDP flood attacks. As Incapsula team continued to block and monitor incoming DDoS commands, they saw that the list of targets went beyond American banks, also including e-commerce and commercial websites from several other countries.
Incapsula published the full description of the DDoS attack in the company blog, concluding it by saying that this was just another demonstration of how security on the Internet is always determined by the weakest link. Simple neglect in manage the administrative password of a small UK site, can very quickly be exploited by Botnet shepherds operating obscurely out of Turkey to hurl large amounts of traffic at American banks.
Incapsula Security Analyst, Ronen Atias said: “This is a good example of how we are all just a part of a shared ecosystem where website security should be a shared goal and a shared responsibility.”
Source : THN
Wednesday, January 9, 2013
Hacking Facebook Password like chaning your our password
Hacker found a way to hack and change your password like, just he used
to change his own password. Confused ? Recently Facebook fix a very
critical vulnerability on the tip of 'Sow Ching Shiong',
an independent vulnerability researcher. Flaw allows anyone to reset
the password of any Facebook user without knowing his last password.
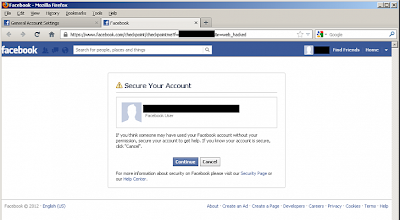
At Facebook, there is an option for compromised accounts at "https://www.facebook.com/hacked"
, where Facebook ask one to change his password for further protection.
This compromised account recovery page, will redirect you to another
page at "https://www.facebook.com/checkpoint/checkpointme?f=[userid]&r=web_hacked" .
Researcher notice that the URL of the page having a parameter called "f"
which represents your user ID and replacing the user ID with victim's
user ID allow him to get into next page where attacker can reset the
password of victim without knowing his last password.
The Vulnerability was very simple to execute, but now patched by Facebook Security Team.
Subscribe to:
Comments (Atom)